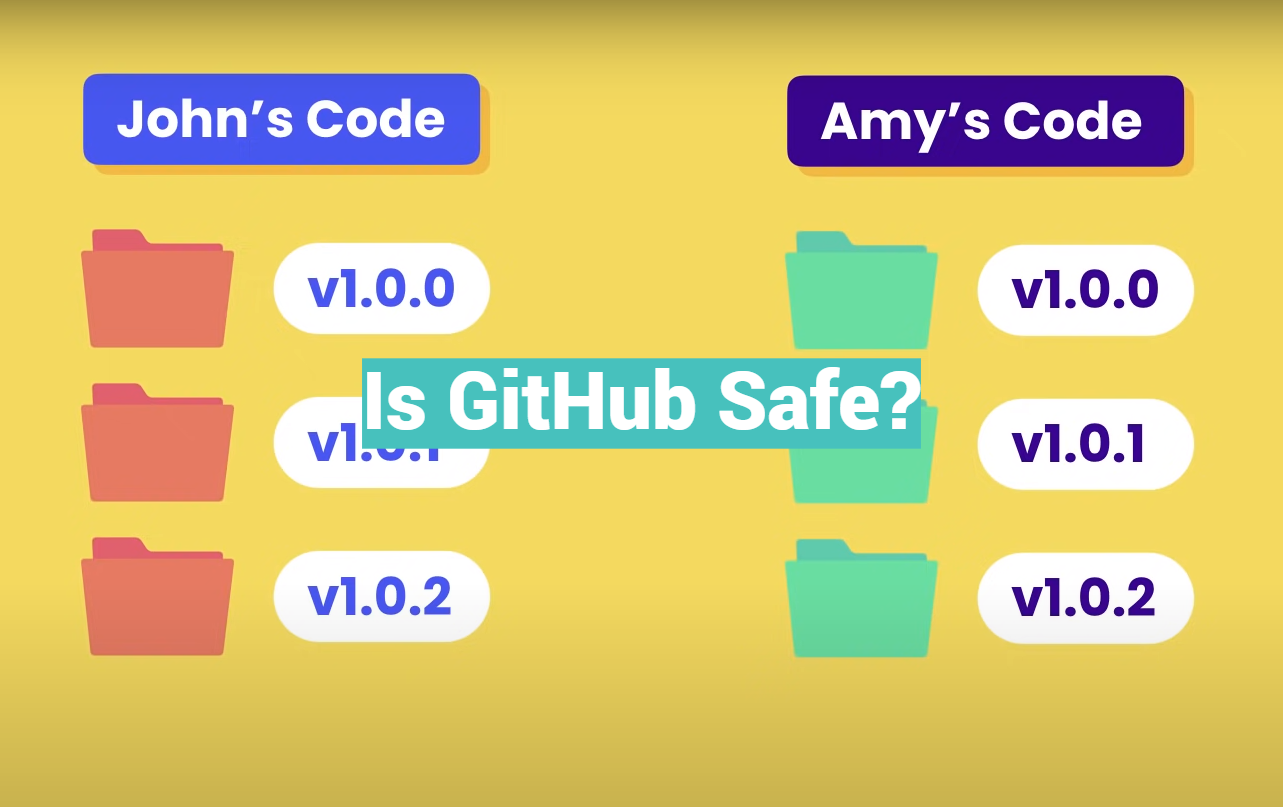
GitHub is one of the most widely used software development platforms in the world, with over 100 million repositories and 56 million users as of 2021 [1]. It has become the go-to platform for developers to collaborate, share, and host their code online. However, with the increasing number of cyber threats and data breaches, many people have raised concerns about the safety and security of using GitHub.
In this article, we will explore the question of whether GitHub is safe to use. We will examine the security features and practices that GitHub employs to protect its users’ data and code. We will also discuss the potential risks that developers may face when using GitHub, such as data breaches, malicious attacks, and accidental code leaks.
To start, we will delve into the security measures that GitHub employs to protect its users. GitHub uses industry-standard encryption to secure users’ data in transit and at rest. It also offers two-factor authentication, which adds an extra layer of security to users’ accounts. GitHub also has a bug bounty program that rewards security researchers who report vulnerabilities or security issues in the platform.
We will then explore some of the potential risks that developers may face when using GitHub. For example, malicious actors may try to steal sensitive data or inject malicious code into repositories. Additionally, developers may inadvertently leak sensitive information or credentials, leading to potential security breaches.
Cyber Threats on GitHub:
1) Hacker Attacks
GitHub is a popular target for malicious hackers and cybercriminals, who use it to launch a range of attacks. Depending on their aim, these can include distributed denial-of-service (DDoS) attacks, ransomware attacks, or the exploitation of vulnerabilities in an application’s code. These types of threats can result in data loss or theft, service disruption, and financial damage.
2) Malware Attacks
Malicious actors may try to spread malware via GitHub repositories by adding malicious code that executes when someone downloads or clones the repository. Malware can also be hidden inside legitimate software programs available on GitHub — attackers may hide Trojan horses or other malicious programs within seemingly legitimate applications.
3) Data Exposure Risks
GitHub allows users to share sensitive data, such as passwords and personally identifiable information (PII). If that information is not stored securely, it may be accessed by malicious actors who can use it for fraud or identity theft. To prevent this from happening, GitHub allows administrators to set permissions on repositories and restrict access using authentication methods.
4) Team Members’ Negligence
Another issue that can arise on GitHub is negligence on the part of team members. For example, a user may accidentally push sensitive data to a public repository or share an unlocked SSH key with the wrong person.
Additionally, users may not have proper access control setup — giving unauthorized users the ability to make changes to their repositories. To prevent these issues, it is important for organizations to provide training and resources to help team members understand best practices when using GitHub [2].
Can Viruses Be Uploaded To GitHub?
No, GitHub does not allow viruses to be uploaded. All repositories and gists are monitored for malicious content and any suspicious code is immediately blocked from being committed. Additionally, all commits and files in a repository are scrutinized by varying levels of security checks that are designed to detect potential issues in the code base.
As such, any malicious or potentially dangerous content is quickly identified and removed before it can cause any harm. This makes GitHub an incredibly safe platform for hosting your code and collaborating with other developers.
GitHub Outages Examples
One example of a significant GitHub outage occurred in October 2018, when the platform experienced a distributed denial-of-service (DDoS) attack. The attack caused the site to be unavailable for several hours, impacting millions of users who rely on GitHub for their development workflows. The attack targeted a specific GitHub repository that was hosting code related to the Great Firewall of China, and it was believed to be a politically motivated attack.
Another example of a GitHub outage occurred in November 2020, when the platform experienced a series of disruptions that caused intermittent service outages for several hours. The outage was caused by a combination of factors, including a surge in traffic due to increased usage during the COVID-19 pandemic and a network configuration issue that caused traffic to be redirected to the wrong data center. The outage impacted users around the world, including developers who rely on GitHub for their daily workflows and businesses that use GitHub as part of their development processes.
In addition to these major outages, GitHub has experienced other smaller-scale disruptions and service outages over the years. These can be caused by a variety of factors, including issues with the platform’s infrastructure, software bugs, or human error. While these outages are generally resolved quickly, they can still impact developers who rely on GitHub for their work [3].
To mitigate the risks of GitHub outages, developers can take several precautions. These include backing up important code repositories and data, using redundant systems or backup platforms, and staying informed about any known issues or disruptions on the GitHub platform. By taking these steps, developers can help ensure that they are able to continue working even in the event of a GitHub outage.
Ways For Developers To Stay Safe On GitHub:
1) Use A Virus Scanner
Using a reliable virus scanner on your computer can help you stay safe on GitHub. Your system should be protected from viruses and malicious software, which can potentially harm your work or steal important information. Be sure to update your virus scanner regularly so that it is up-to-date with the latest security threats.
2) Avoid Clicking On Unfamiliar Links
When using GitHub, watch out for unfamiliar links. Some malicious links may try to infect your device or direct you away from secure sites. It’s best to avoid clicking on any suspicious links and only visit websites that are trusted by you and other developers in the community.
3) Protect Your Login Credentials
It’s important to protect your login credentials from unauthorized access. Use a strong password and keep it confidential. If possible, use two-factor authentication to add an extra layer of security to your account. Additionally, change your password regularly and don’t reuse passwords between different websites or services.
4) Be Cautious With Forking Projects
When forking a project on GitHub, be sure to check out the source code thoroughly before making any changes or additions. Make sure that the code is secure and doesn’t contain any malicious code that could potentially harm your system. This step is especially important if you are using third-party projects to avoid potential security issues or data breaches.
5) Tighten Your Repo Settings
If you are hosting private repositories on GitHub, it’s important to enable additional security measures. You can set up restrictions to limit or control access to your repository, such as adding an extra layer of authentication for users who want to view the code or edit the project. Additionally, use features like two-factor authentication and IP whitelisting to further protect your account from unauthorized access.
6) Remove Sensitive Data
Make sure to remove any sensitive data that you don’t need from your repositories. This includes personal information, passwords, API keys, and other confidential details. Additionally, check that your code isn’t publicly visible or accessible by attackers.
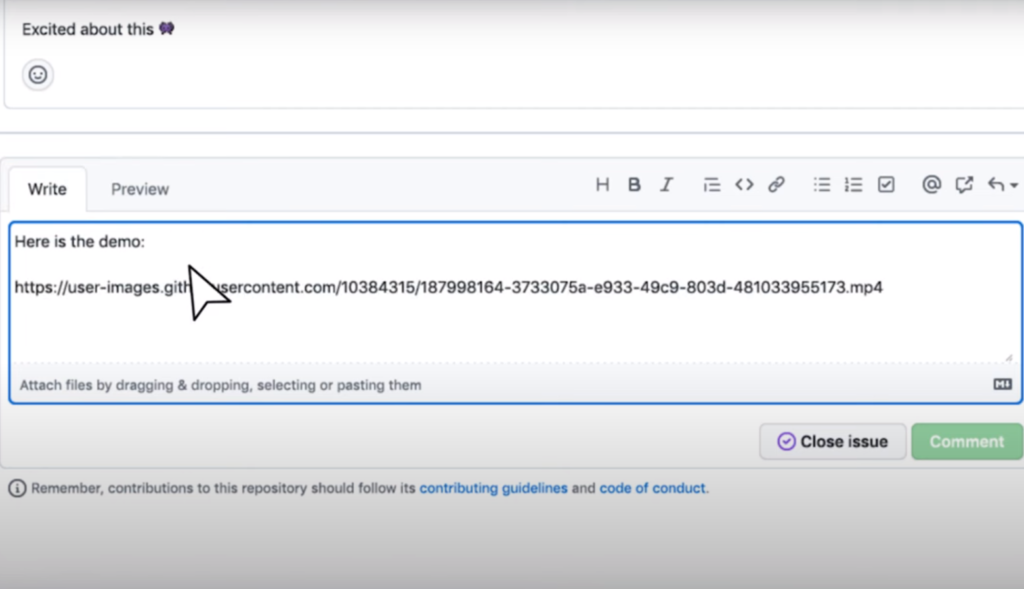
7) Look To The Community
GitHub has a large and active community of contributors, developers, and security experts. If you have any questions or concerns about staying safe on the platform, reach out to other users for help. Furthermore, read up on security best practices and articles from reputable sources so that you can stay informed about potential threats.
8) Inspect The Repository
Before downloading any repository from GitHub, take a few moments to inspect the code. Look for any suspicious links or files that could be malicious. Additionally, consider auditing the source code and verifying its authenticity before using it in your projects. This can help you avoid potential security issues and data breaches [4].
How To Minimize The Risk Of GitHub Data Loss?
GitHub is generally a safe platform to store your data, however, there are still some things you can do to minimize the risk of data loss. Some of these include:
- Regularly back up your data. GitHub only keeps snapshots of the code at certain points in time, so it’s important that you regularly back up your data so that if any changes are made, you have the original version on hand;
- Use strong passwords and two-factor authentication. This will help protect your account and data from unauthorized access or malicious activity;
- Be sure to read GitHub’s Terms of Service and familiarize yourself with their policies regarding ownership and usage of content stored on their platform;
- Understand the implications of open-source code and make sure to respect any licenses or copyrights associated with your code;
GitHub Backup With GitProtect
Git Protect is a service that provides backups for GitHub repositories. It’s an additional layer of security for your code, giving you peace of mind knowing that all your hard work is stored securely and can be easily restored if needed. It also allows you to roll back changes quickly in the event of a mistake or system failure.
The Git Protect backup process is simple: it runs periodically and stores a copy of your repository as a zip file on its secure servers [5]. This means even if something goes wrong with your original repository, you’ll have a reliable backup ready to go!
Plus, Git Protect offers extra features like email notifications when new commits are made to your repository – so you know right away when there’s been any activity. All this makes Git Protect the perfect way to keep your code safe and secure!
Risk Of GitHub For Developers:
Leaks Of Sensitive Company & Customer Data
One of the biggest risks of using GitHub is the potential for leaks of sensitive company and customer data. GitHub repositories often contain code that can reveal proprietary information, such as passwords, API keys, or other sensitive data. If this information falls into the wrong hands, it can lead to significant consequences, including financial loss, reputation damage, and legal liabilities.
GitHub Getting Breached Or Hacked
Although GitHub has robust security measures in place, no system is entirely immune to attacks. A breach or hack could result in the exposure of sensitive information, as well as unauthorized access to the platform by malicious actors.
Someone Stealing Your Password Or Hacking Into Your Account
This could happen due to various reasons, such as using weak passwords, sharing credentials with others, or falling for phishing scams. If an attacker gains access to a developer’s account, they could alter code, delete repositories, or commit malicious code that could harm the entire project.
Developer & Employee Negligence
Developer and employee negligence is also a significant risk when it comes to using GitHub. In some cases, developers may accidentally commit sensitive information or leave repositories public that should be private. Additionally, employees may fail to follow proper security protocols, such as regularly updating their passwords or using multi-factor authentication, which can put the entire organization at risk.
The Misuse Of Public Repositories By Employees Or Contractors
Employees may accidentally or intentionally upload code that is not intended to be public, leading to sensitive information being exposed. Contractors or third-party vendors may also misuse public repositories, either by accident or maliciously, leading to similar issues.
Recommendations: How Companies Can Prevent GitHub Leaks
Only Use Private Repositories
The most important thing companies need to do to prevent GitHub leaks is to only use repositories that are marked as private. Private repositories require anyone who wants access to go through a process of requesting access authorization. This makes it much more difficult for outsiders, including hackers and malicious actors, to gain access without being detected. Additionally, private repositories can be set up with additional security settings such as two-factor authentication and IP address restrictions that can help provide an extra layer of protection against unauthorized access.
Educate Employees On Security Best Practices
In addition to having the right technical infrastructure in place, it is also important for companies to make sure their employees understand proper security best practices when using GitHub. Educating your staff on how to securely handle confidential information, as well as the risks associated with using GitHub for sensitive data, is essential to preventing leaks. Additionally, companies should have policies in place that clearly define how confidential information should be handled and stored on GitHub.
Use Strong Passwords & 2FA
To ensure that your account remains secure, make sure to use a strong password and enable two-factor authentication (2FA). A strong password should be at least 8 characters in length and contain a combination of upper and lower-case letters, numbers, and symbols. It’s also helpful to use a unique password for each online account you have.
Delete Old Accounts
When it comes to staying safe on GitHub, one of the most important steps is deleting any old accounts that are no longer used. This helps reduce the chances of a hacker gaining access to your information and using it without permission. It also prevents data breaches if someone were to get access to an outdated account.
To delete an account, log in and select “Delete Account” from the settings menu. Then follow the instructions provided to complete the process. Deleting unused accounts can help ensure that your information stays secure on GitHub.
Vet Who You Hire
When seeking new employees, it’s important to vet who you hire. It is essential for employers to do research on potential candidates and check references, as well as monitor all future activities of those they hire. This includes keeping an eye on their GitHub accounts. Knowing who your team works with is key; if someone has questionable connections or questionable content in their account, that could lead to legal problems down the road.
Backup Your Repository
GitHub provides a reliable service but it is still important to perform regular backups of your repositories. Keeping an up-to-date backup can help you recover from data loss or security breaches quickly and easily. You should also keep track of any sensitive information stored in the repository, including access tokens and passwords, as these could be targeted by malicious actors. Additionally, if you ever need to move your codebase elsewhere, having a backup makes the process much easier.
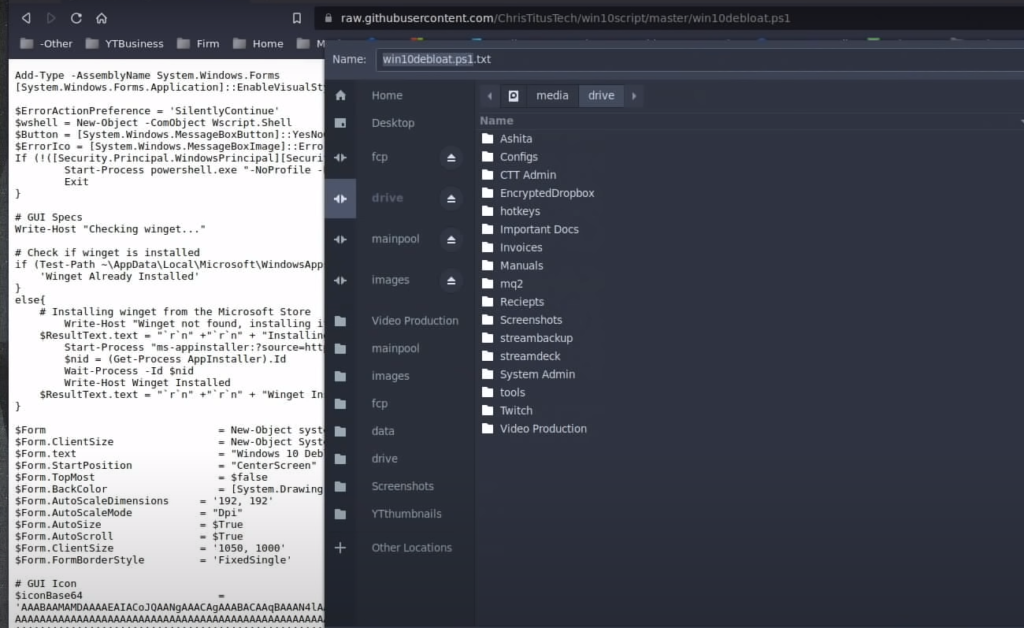
Only Download From Trusted Repositories
When it comes to downloading applications from GitHub, the same safety rules apply as when downloading any other software. Be careful not to download from untrusted sources, and make sure that you’re getting the latest version of the software.
Be Careful About Updates
Outdated versions of the platform may have security vulnerabilities that can be exploited by malicious actors. Make sure you install all available updates promptly to protect yourself and your data from potential attacks. Also, you need to download official applications or plugins from trusted sources to avoid any malware or malicious code being installed on your system.
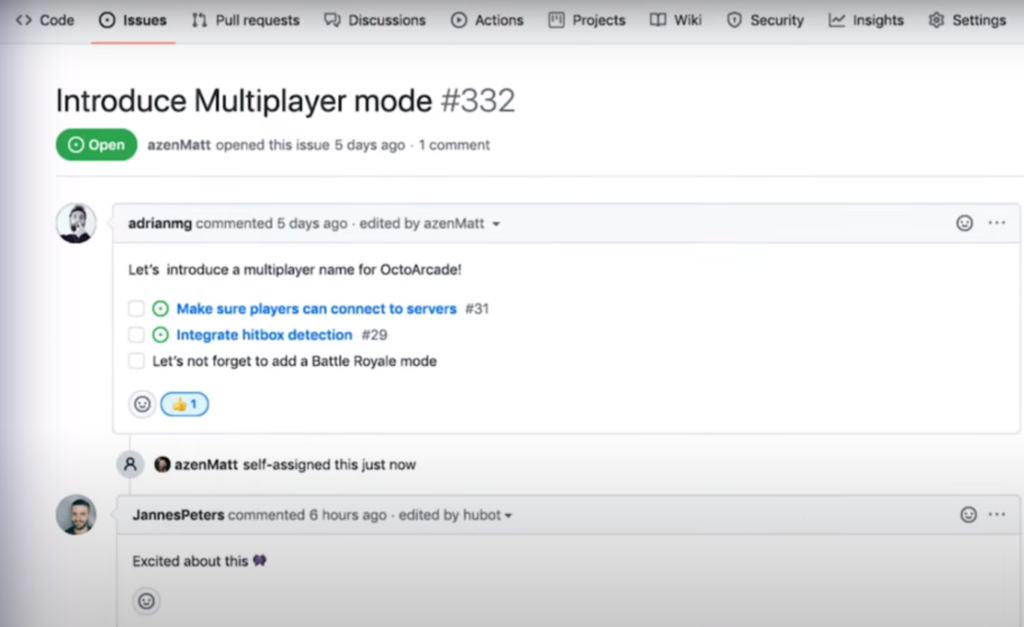
Make Sure The Project Is Updated And Issues Are Fixed
One of the important things to consider when assessing whether GitHub is safe is the project’s maintenance status. It’s important to look at when the project was last updated and how frequently any issues are addressed.
If a project has not been updated in a long time, or if there are unresolved issues that have been around for weeks or months, then it’s probably best to stay away from that particular repository. It might be that the developers are no longer actively working on it, leaving it vulnerable to potential security flaws and exploits.
On the other hand, if a project has frequent updates from its maintainers and issues are regularly addressed, then you can rest assured that the code will be secure and reliable.
Use A Strong Antivirus & Firewall
As an extra precaution, it’s important to make sure your computer itself is protected with the best antivirus and firewall protection available. This will help keep malicious software from infiltrating your personal information.
Make sure you always update your software whenever possible as security updates are often released to plug any potential vulnerabilities in existing systems. With these precautions in place, you can rest assured that GitHub is a safe platform for sharing and collaborating on projects online.
Tools All Developers Should Use & Know About:
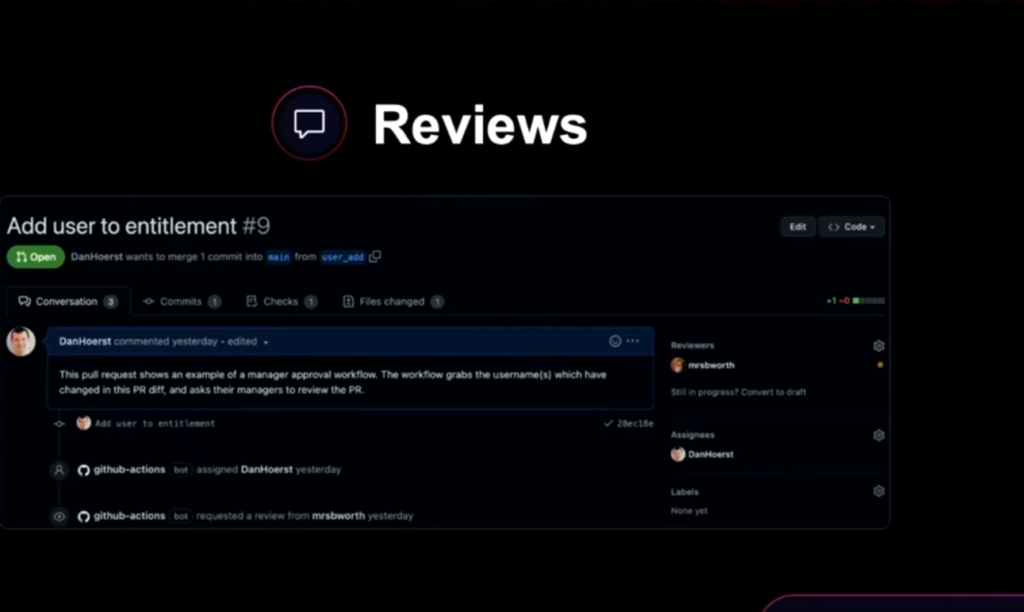
1) GitHub Security
GitHub is a popular platform for hosting and managing source code repositories. It offers various features and tools to streamline the development process and enhance collaboration among team members. One of the essential features of GitHub is security. GitHub has a built-in security system that helps to keep the code and the repository secure from external threats.
GitHub security includes features like vulnerability alerts, dependency graphs, code scanning, and secret scanning. With vulnerability alerts, GitHub automatically detects security vulnerabilities in the repository’s dependencies and sends an email notification to the repository’s owner. A dependency graph helps to visualize the dependencies used in the repository, making it easy to track and manage them.
Code scanning is an automated process that checks the code for security vulnerabilities, coding errors, and other issues. Secret scanning, on the other hand, helps to detect and remove secrets like passwords and API keys from the repository, ensuring that they do not fall into the wrong hands.
2) Vault Project
The Vault Project is a security tool for developers to securely store, manage and share sensitive information such as passwords and access codes. It is based on a system of roles that give each user different levels of access. This helps protect against unauthorized access and reduces the risk of data leakage. It also provides tools like audit logging to track who has accessed or changed information in your Vault project.
3) Whitesource Bolt
Whitesource Bolt is a powerful open-source security scanning tool that can help developers detect and fix known vulnerabilities in their code. It uses automated scans to identify potential security holes within your project code, allowing you to address them quickly and efficiently [6].
4) GitHub Security Alerts
GitHub Security Alerts are notifications that let you know if there are any known vulnerabilities in the dependencies used by your project. These alerts allow you to take action quickly before an attack takes place, giving you peace of mind when it comes to the safety of your projects on GitHub.
5) Snyk
Snyk is a security tool specifically designed for developers who use open-source software in their projects. It scans your project code for vulnerabilities and then offers actionable steps to fix them. Snyk also provides advice on best practices for secure coding, making it a great resource for developers looking to improve their security knowledge.
FAQ:
- How do I know if a GitHub is safe?
You can evaluate the safety of a GitHub repository by checking if it is hosted by a trustworthy organization or individual if it has a history of malicious activity or security breaches if it has a large number of contributors or stars, and if it is well-maintained with regular updates and security patches. Also, you can examine the source code for any suspicious or malicious code, and use antivirus software to scan for any potential threats.
- Is malware allowed on GitHub?
No, malware is not allowed on GitHub. The platform has policies in place to prohibit the hosting of malicious software and actively monitors repositories for any violations. Users are encouraged to report any suspected malware or security threats to GitHub’s support team.
- Can someone steal my code on GitHub?
Someone can steal your code on GitHub if you have not taken appropriate measures to protect it. However, GitHub offers features such as private repositories, two-factor authentication, and access control that can help mitigate the risk of theft. It is also important to license your code appropriately so that you retain ownership and legal rights to your work.
- Is GitHub owned by Microsoft?
Yes, GitHub was acquired by Microsoft in 2018 [7].
- Can anyone see my GitHub?
By default, all public repositories on GitHub can be viewed by anyone with internet access. However, you can choose to make your repositories private, which restricts access only to authorized collaborators.
- Is copying code from GitHub safe?
Copying code from GitHub can be safe, as long as the code is properly licensed and does not violate any copyright or intellectual property laws. However, it is important to thoroughly review the code and ensure that it meets your specific needs and to attribute credit to the original author if required.
- Is GitHub safe for students?
Yes, GitHub is generally considered safe for students to use, as long as appropriate security measures are taken and students adhere to ethical coding practices. GitHub offers free educational resources and tools to help students learn coding skills and collaborate with others in a safe and secure environment.
- Why do hackers use GitHub?
Hackers may use GitHub to store and share malicious code, as well as to collaborate with other hackers on developing and improving their techniques. However, it is important to note that GitHub actively monitors for any security threats and takes steps to remove any malicious repositories.
- Can GitHub users see your email?
GitHub users can see the email associated with your account if you choose to make it public, but you can also choose to keep your email private. Additionally, GitHub provides a feature called “noreply” email, which allows you to keep your email address private while still receiving notifications and messages from the platform.
- Is GitHub blocked in any country?
GitHub has been blocked in some countries in the past, such as China and Russia, but it is generally accessible in most parts of the world.
- Can GitHub projects have viruses?
GitHub projects can potentially have viruses if they contain malicious code or are developed with malicious intent. However, GitHub actively monitors for any security threats and takes steps to remove any malicious repositories.
- Is GitHub used for spying?
GitHub is not intended for use in spying or espionage, and any such activities are prohibited by the platform’s terms of service. GitHub actively monitors for any suspicious activity and takes steps to prevent abuse.
- Is it safe to store keys on GitHub?
Storing keys on GitHub is generally not recommended, as it can pose a security risk if the repository is public or if the keys fall into the wrong hands. Instead, keys should be stored securely on your local machine or a secure server.

- How do I stay anonymous on GitHub?
Staying completely anonymous on GitHub can be challenging as the platform requires users to have an account to create and publish repositories.
However, users can take some steps to minimize the amount of personal information they share on GitHub, such as:
- Choose a username that does not reveal your real name or personal information;
- Use a private email address that is not linked to your real identity;
- Do not disclose personal details in your public profile or repository descriptions;
- Use a VPN or Tor to mask your IP address when accessing GitHub;
- Be mindful of the content you upload and avoid including sensitive information;
- Does GitHub collect data?
Yes, GitHub collects user data to improve its services and provide relevant recommendations. The platform collects information such as IP addresses, browser type, device type, operating system, and usage data such as the time and date of user actions on the site. GitHub also uses cookies and other tracking technologies to collect user data.
- What is the disadvantage of using GitHub?
The main disadvantage of using GitHub is that it is a centralized platform, meaning that all the data and control are in the hands of the company. This centralized approach could lead to issues such as data breaches, censorship, and loss of data. Additionally, GitHub is primarily used for open-source projects, which may not be suitable for proprietary or confidential projects.
- Does Google look at your GitHub?
Google, as a company, can technically access any public information on GitHub, including your public repositories, commit history, and contributions. However, whether or not they look at your GitHub depends on the context.
For example, if you are applying for a job at Google, the hiring manager or recruiter may look at your GitHub profile as part of the application process. In this case, they may be interested in seeing your coding skills, projects you have worked on, and contributions to open-source projects.
On the other hand, if you are just a regular user of Google services (e.g., Google search, Gmail, etc.), Google is unlikely to actively seek out your GitHub profile. They may only access your GitHub data if it is necessary for a specific feature or service they offer, such as integrating with your GitHub account for authentication purposes.
Useful Video: What is Git? Explained in 2 Minutes!
References:
- https://github.com/security
- https://gitprotect.io/blog/is-github-a-safe-place-for-your-source-code/
- https://rewind.com/blog/is-github-still-safe-to-use/
- https://rigorousthemes.com/blog/is-github-safe-to-use/
- https://www.reddit.com/r/NoStupidQuestions/comments/4z1qw5/is_github_safe_to_download_from/
- https://linuxhint.com/is-github-safe-for-source-code/
- https://developerpitstop.com/is-github-safe/


Leave a Review